SonicWALL – HILDACRYPT RANSOMWARE ACTIVELY SPREADING IN THE WILD
The SonicWall Capture Labs Threat Research Team observed reports of a new variant family of Hildacrypt ransomware [Hildacrypt.RSM] actively spreading in the wild.
The Hildacrypt ransomware encrypts the victim’s files with a strong encryption algorithm until the victim pays a fee to get them back.
Infection Cycle:
The ransomware adds the following files to the system:
- Malware.exe
- % App.path%\ TXT
- Instruction for recovery
- %App.path%\ [Name]. HILDA!
- % App.path%\ TXT
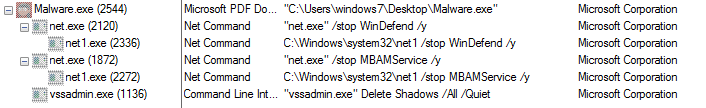
Once the computer is compromised, the ransomware runs the following commands:
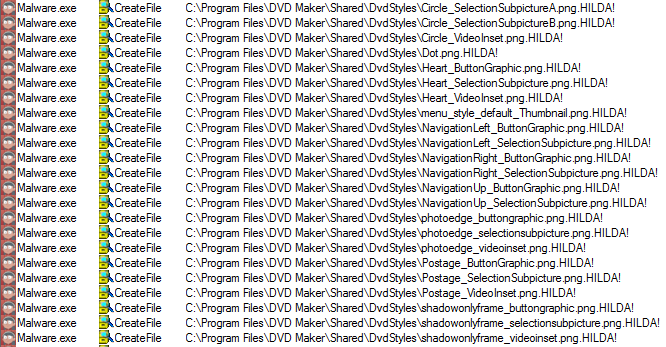
The ransomware encrypts all the files and appends the [.HILDA!] extension onto each encrypted file’s filename.
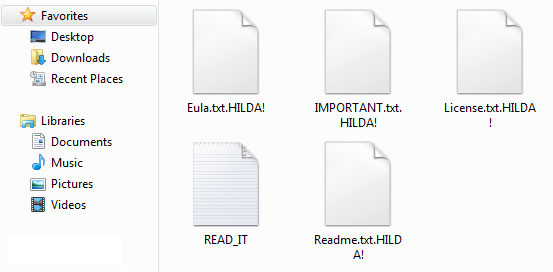
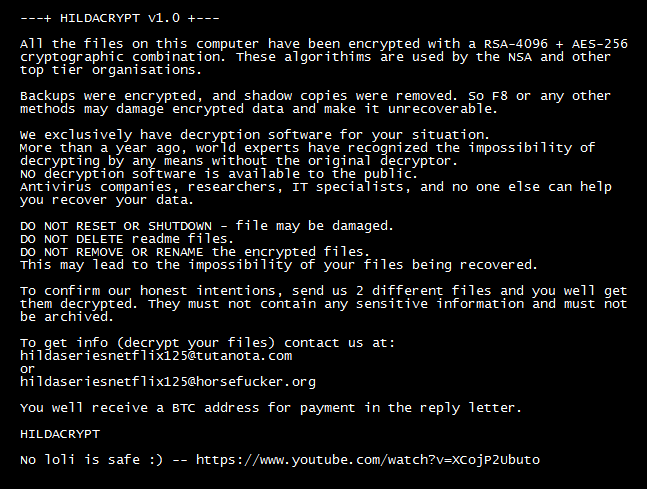
After encrypting all personal documents, the ransomware shows the following text file containing a message reporting that the computer has been encrypted and to contact its developer for unlock instructions.
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Hildacrypt.RSM (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.











Dell Software Group sold to help fund looming EMC deal
Ingram Micro gets distribution access to Dell’s security range in Australia