Tokyo Olympics Leveraged in Cybercrime Attack

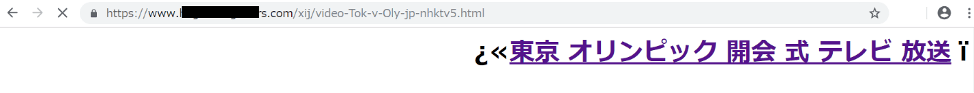
Just before the opening of the Tokyo Olympics, we confirmed an attack that directed users from a fake TV broadcast schedule page to browser notification spam.
*Updated on July 26 (Original release date July 19)
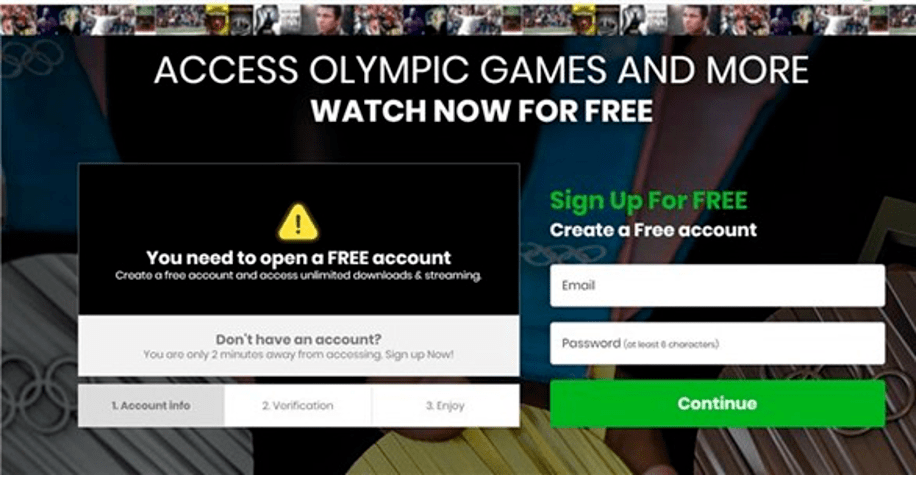
As of the 26th of July, a fake page that leads to a suspicious sports broadcasting site of the same type has been confirmed by web search. In addition to the browser notification spam, we have also confirmed a method of making users register their personal information such as email addresses on suspicious sites under the pretense of watching videos. It is believed that similar methods of leading people to suspicious sites will continue in the future. It is important to be aware of such schemes to avoid being deceived.
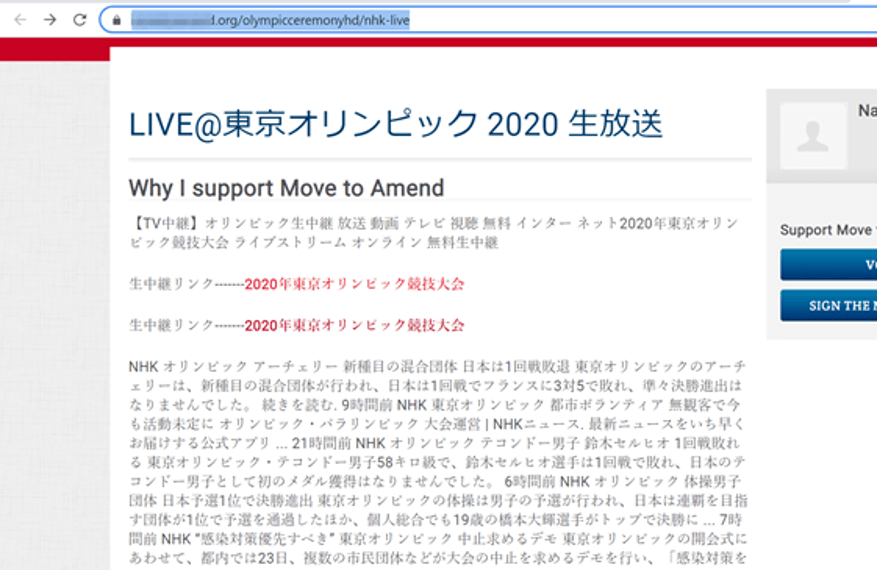

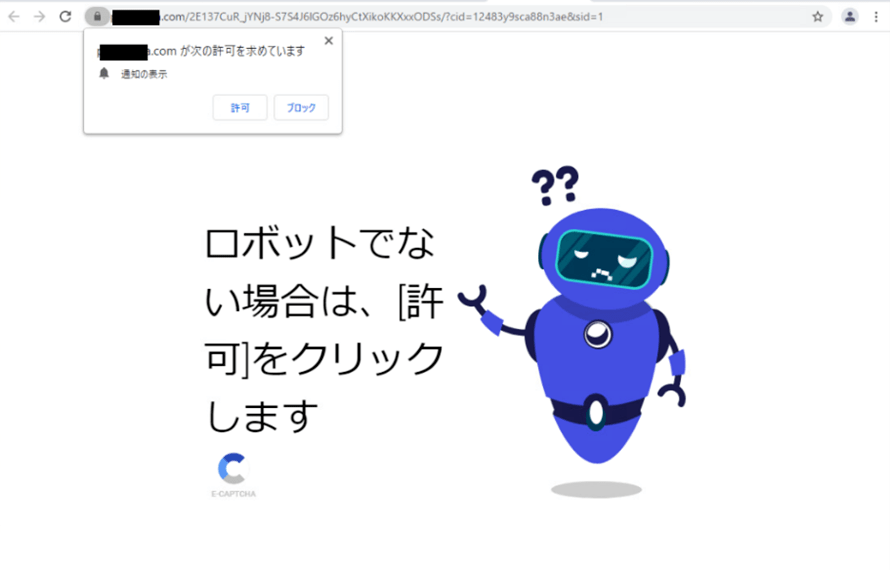
On July 19, just before the opening of the Tokyo Olympics, Trend Micro confirmed a case where a web page disguised as a TV broadcast schedule for the Tokyo Olympics was directing to a suspicious sports broadcast site. According to a Trend Micro survey on Thursday, this suspicious sports broadcast site was directed to so-called “browser notification spam”, which allows users to be notified of browsers and displays malicious advertisements.
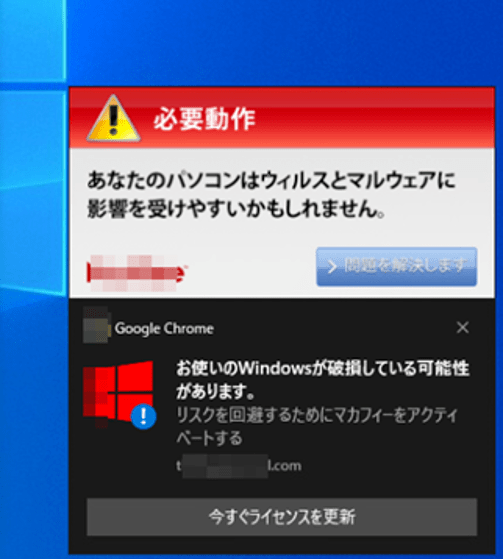
In addition, we have confirmed that there are several fraudulent web pages disguised as TV broadcasting schedules related to the Tokyo Olympics, which appear to have been created to lead users to this suspicious site. From the wording used, it is presumed that these fake pages were created in order to appear in the search results when ordinary users search the web to check the impending TV broadcast of the Olympics. However, as of 12:00 a.m. on July 19, these pages were no longer displayed in Google search results, indicating that the cyber criminals’ plan has already been derailed.

In the past, whenever a global event such as the Olympics is held, there have been cybercriminals who try to take advantage of the buzz.
Threats to the Olympics
As we have reported in the past on various Olympic-related threats, the Olympics, like other large-scale sporting events, has become a target for cybercriminals to take advantage of. Compared to other threats that take advantage of global events, Olympic threats are not much different in terms of methods, but rather cybercriminals are using traditional tactics to take advantage of popular online searches and events related to the Olympics. It’s more like cybercriminals are taking advantage of traditional tactics. Past Olympic threats have used a variety of tactics, including the following:
- Emails and messages containing Olympic-related topics that lead to malicious sites or attachments that can be opened
- Using SEO poisoning, links to phishing sites and other malicious sites are displayed at the top of search results pages when searching for Olympic-related keywords. General users can easily believe that these sites are legitimate, and suffer damage such as having their personal information collected from the sites they visit, or being infected with malware.
If you are a fan of the Olympics and encounter one of these threats, you could suffer a great deal of damage without even realizing it. Malware can be created on a user’s computer by a defaced sports site, spam email messages can contain malicious links and attachments, and fake video streaming sites can prompt users to purchase fake security software. In other words, it’s not a good idea.
Another possible scam is to offer Olympic-related items that are not normally given away for free, and to lure users by claiming that they are available at a special discount. As a result, the user may suffer financial damage due to the fake purchase procedure, and the personal information entered may also be collected.
Olympic-related information can be obtained from official Olympic sites, sponsor sites, etc. Be careful not to click on Olympic-related links via e-mail, instant messenger (IM), or social media messages. It’s also important to note that cyber criminals will not be able to get to your SEO page. It is also important to note that cyber criminals use SEO poisoning tactics to display malicious links at the top of search results pages. These malicious links can lead users to malware infections or to specially crafted websites and web pages. An example of this is the case of the Vancouver 2010 Winter Olympics. In this case, a malicious link was displayed at the top of the search engine results page. The malicious link pretended to be a site to update Windows Media Player, but in fact, it contained a malware.
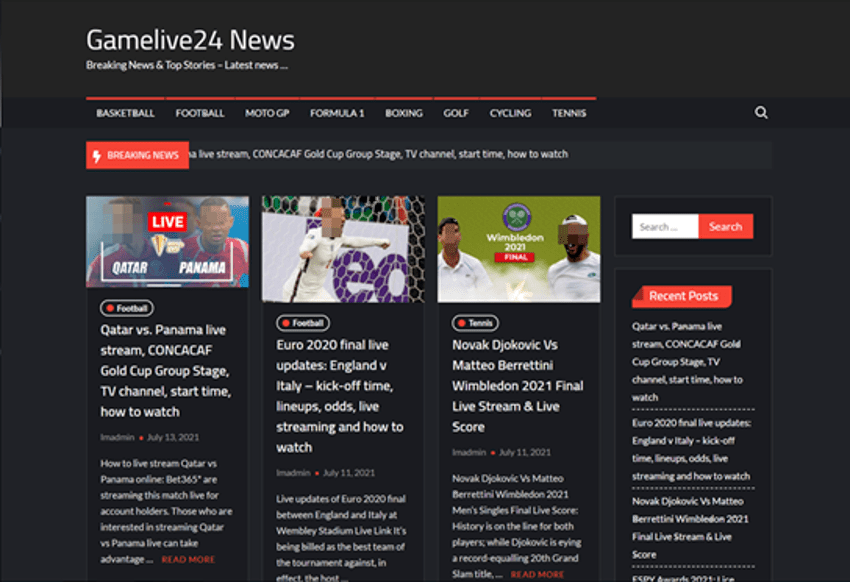
In the past Olympics, we have seen fake ticket sale sites and fraudulent sites that use free tickets as bait. However, the Tokyo Olympics will be held without spectators in many venues, so the same tactics will not work. Instead, the possibility of fake sites such as TV broadcasts and streaming Internet distribution will increase.
Here is a summary of other possible Olympic-related cybercrime tactics
- During the Games: fake live streaming and videos, Twitter hashtag hijacking, scams using scandalous images of Olympic athletes and social networking accounts, fake apps, etc.
- Post-closing: Scams that use the words and deeds of Olympic athletes as well as auctions of their personal belongings.
How to Avoid Being a Victim
Considering the possibility of advertisements and suspicious sites being included in web search results through methods such as SEO poisoning, it is safer to directly browse official sites that you have bookmarked in advance or news sites that you use on a regular basis. If you use search sites, you may be able to avoid suspicious sites by carefully checking the URLs of search results. If you want to watch the Olympics via the Internet, the first thing you should be aware of is that you should only watch the games streaming from the official sites or affiliated sites. For this year’s Tokyo Games, NHK+, gorin.jp, and TVer are the official streaming sites. Lesser-known streaming sites, especially those that claim to be “unrestricted video sites,” are likely to be traps set by cyber criminals, and you should be very careful when clicking on them. Inadvertently clicking on such sites may result in the infection of malware or the fraudulent acquisition of personal information.
Trend Micro’s Countermeasures
Countermeasures against fake websites: Trend Micro uses Web Reputation System (WRS) technology to block fraudulent sites such as fake sites and phishing sites that have been used to promote the Olympics. In addition, phishing e-mails that lead to unauthorized sites are filtered using E-Mail Reputation (ERS) technology.











Dell Software Group sold to help fund looming EMC deal
Ingram Micro gets distribution access to Dell’s security range in Australia